In today’s digital landscape, the integrity of professional networks, such as the one identified by 8339322075, is increasingly under threat. Cybercriminals employ sophisticated tactics that compromise sensitive data and disrupt operations. The need for comprehensive security measures has never been more critical. Organizations must evaluate their current defenses and consider how emerging vulnerabilities could impact their infrastructure. Understanding these dynamics is essential for fostering a resilient security posture. What strategies will prove most effective in this ongoing battle?
Understanding the Importance of Digital Network Security
As organizations increasingly rely on digital infrastructure to operate and communicate, the significance of robust network security becomes paramount.
Essential components include data encryption, which protects sensitive information from unauthorized access, and effective firewall management, which acts as a barrier against external threats.
Together, these strategies not only safeguard data integrity but also empower organizations to maintain operational continuity and uphold user privacy.
Key Threats to Professional Digital Network 8339322075
The vulnerability of professional digital networks to various threats underscores the critical need for comprehensive security strategies.
Key threats include phishing attacks, which deceive users into divulging sensitive information, and ransomware threats, which can incapacitate systems and demand payment for restoration.
These risks emphasize the necessity for organizations to implement robust defenses to safeguard their digital operations and protect valuable data from exploitation.
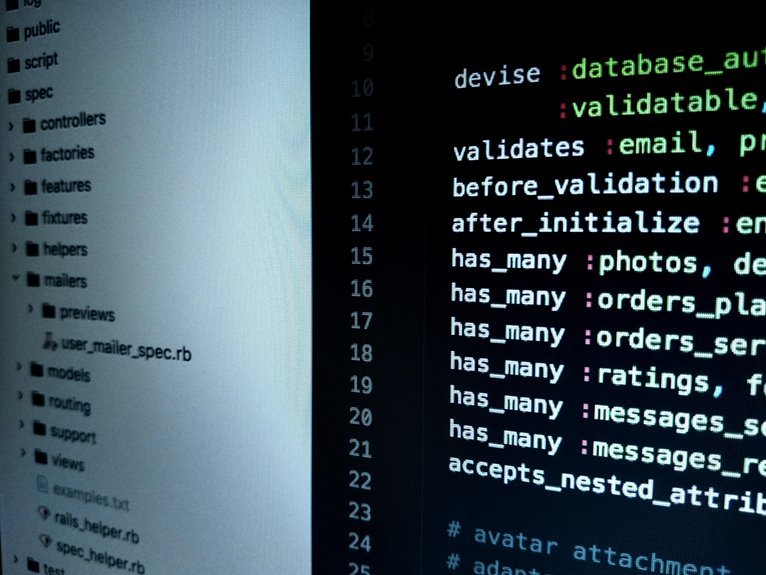
Essential Security Measures for Protecting Your Network
To effectively safeguard a professional digital network, organizations must adopt a multifaceted approach that encompasses a variety of essential security measures.
Proper firewall configurations are vital to filter unauthorized access, while robust encryption protocols ensure that sensitive data remains confidential during transmission.
Implementing these strategies not only fortifies the network against potential breaches but also empowers users with the freedom to operate securely.
Best Practices for Maintaining Long-Term Security and Compliance
Sustaining long-term security and compliance within a digital network necessitates a strategic framework that integrates continuous monitoring, regular audits, and employee training.
Implementing robust long-term strategies ensures alignment with compliance frameworks, mitigating risks effectively. Organizations should prioritize adaptive technologies, risk assessments, and clear policies, fostering a culture of security awareness.
This proactive approach not only safeguards assets but also enhances organizational resilience in a dynamic digital landscape.
Conclusion
In conclusion, the theory that robust digital network security is merely a reactive measure is increasingly debunked. Instead, it is evident that proactive strategies, including continuous monitoring and employee education, are vital in combating evolving cyber threats. By embracing a comprehensive security framework, organizations not only protect sensitive information but also foster resilience against potential breaches. Ultimately, the commitment to ongoing security measures is essential for maintaining operational integrity and ensuring compliance in a dynamic digital landscape.